What Should Training Cover?
When suggesting that someone needs more training, consider what specific points should be covered.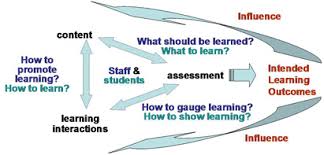
Chris Eng said "Someone should set up a GoFundMe to send whoever wrote the hit piece on password managers to a threat modeling class."
And while it's pretty amusing, you know, I teach threat modeling classes. I spend a lot of time crafting explicit learning goals, considering and refining instructional methods, and so when a smart fellow like Chris says this, my question is why?
Is this "threat modeling as our only hope?" That's when we take a hard security problem and sagely say "better threat modeling." Then we wander off. It's even better with hindsight.
Or is there a particular thing that a student should be learning in a threat modeling class? There was a set of flaws where master passwords were accessible in memory, and thus an attacker with a debugger could get your master password and decrypt all your passwords.
I'm not going to link the hit piece because they deserve to not have your clicks, impressions, or ad displays. It asserted that these flaws mean that a password manager is no better than a text file full of your passwords.
Chris' point is that we should not tell people that using a password manager is bad, and I agree. It's an essential part of defending against your passwords being leaked by a third party site. An attacker who can read memory can read memory, which includes backing stores like disk; in fact, reading disk is easier than reading RAM.
So to loop this around to threat modeling, we can consider a bunch of skills or knowledge that could be delivered via training:
- Enumerate attacker capabilities. "An attacker who can run code as Alice can do everything Alice's account can do." (I am, somewhat famously, not a fan of "think like an attacker", and while I remain skeptical of enumerating attacker motivations, this is about attacker capabilities.)
- Understand how attacks like spoofing can take place. Details like password stuffing and how modern brute force attacks take place are a set of facts that a student could learn.
- Perform multiple analyses, and compare the result. If "what can go wrong" is "someone accesses your passwords by X or Y," what are the steps to do that? What part of the defenses are in common? Which are unique? This is a set of tasks that someone could learn.
I structure classes around the four-question frame of "what are we working on, what can go wrong, what are we going to do, did we do a good job." I work to build up skills in each of those, show how they interact, and how they interact with other engineering work. I think asking 'what else could that attacker do with that access' is an interesting sub of question 2. How attacks work and a selection of real world attacks is something I've done for non-security audiences (it feels like review for security folks). The third, comparing between models, I don't feel is a basic skill.
I'm curious: are there other ways in which a threat modeling class could or should help its students see that 'password managers are no better than text files' is bad threat modeling?
Image (model) from Flinders University, Key elements and relationships in curriculum [link to http://www.flinders.edu.au/teaching/teaching-strategies/curriculum-development/curriculum-process.cfm no longer works]