Appsec roundup - April 2026
The importance of slow time in work is a theme for April, along with how Claude optimized away its own security rules. Also fun games collected at RSA!
This month leads off with Buying Back Our Slack and Which Way Is Downhill?, both by Ryan Moser. The first considers the impact on AI on work, the second how people work in large systems. (I would argue slightly with the framing of the first: work like building a deck or writing tests are not “cognitive rest” but a chance to reflect on our work and “sensemake.”)
Both have a great deal to say about application security, if you take time and think about them. But if you don’t want to do that, articles by Stephen de Vries, the Cloudflare sandbox, and Robert Hansen’s Thoughts on PQC are all thoughtful bits. On the other hand, NIST doesn’t have time to stop and think about all the vulnerabilities anymore.
Threat Modeling
- Andrew Nesbitt has a pair of posts: Package Security Problems for AI Agents, and Package Security Defenses for AI Agents, with separate advice for those using AI coding platforms, and those designing them. Nice!
- Stephen de Vries at ThreatModeler makes a case worth reading in Calm in the Chaos: Why Threat Modeling Matters More as AI Speeds Up the Build-Exploit-Patch Cycle: AI is accelerating code generation, vulnerability discovery, and exploit development, but speed isn't the same as progress. The build-exploit-patch cycle is faster now, not better. Threat modeling, grounded in architectural design before the code is written, is how you break that cycle.
Appsec
- Kenton Varda, Sunil Pai, and Ketan Gupta write on the Cloudflare blog about Sandboxing AI agents, 100x faster, offering Javascript in that sandbox with a virtualized mini filesystem. Neat!
- Vulnerability Research Is Cooked amplifies what I said in February, about a Vulnerability Finding Inflection Point.
AI
- Adversa.ai writes about how Claude Code vulnerability: Deny rules silently bypassed because security checks cost too many tokens. Oops!
- See above “Vuln finding inflection point” for my February comments about Glasswing and Mythos.
Regulation
- NIST has announced that they're going to enrich a smaller subset of CVEs with NVD data.
Quantum 🔥
- Robert J. Hansen has Thoughts on PQC (Post Quantum Cryptography). He is not kind to people who have gone beyond earning skepticism to earning scorn.
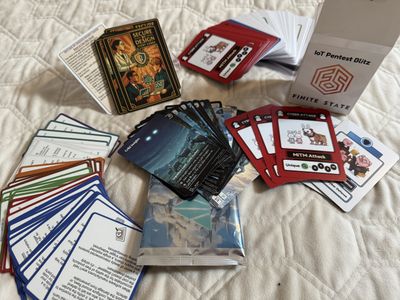
Games Received
- Finite State’s Pentest Blitz.
- Bob Lord’s Secure By Design Storycards.
- A set of Magic: The Gathering cards which I believe are from Cribl, but they’re very minimally branded and I can’t find anything about them online.
Shostack + Associates News
- We’re getting ready for Threat Modeling AI Systems, delivered by the awesome team of Michael Novack and Shoshana Cox in Washington DC, May 19+20. You can read Mike’s blog post announcing the course.
- We rebranded for April 1. You can see the Star Trek version of our homepage.
- Adam will be presenting “Threat Modeling in the Age of AI” at Vancouver’s VanSecSIG on May 8.
- Adam and Erik will be delivering our classic Threat Modeling Intensive at OWASP Appsec EU in Vienna, June 23-24.
- Adam and team will be delivering Threat Modeling Intensive with Complete AI at Blackhat August 1-4.
- The Global Encryption Coalition released Open Letter on [Canada’s] Bill C-22, An act respecting lawful access. Adam was honored to sign.
- A research team including Ruhr University Bochum, Ludwig-Maximilians-Universität München, and the University of Washington is doing a research project on how security decisions are made in complex software projects, and we’re recruiting for participants. Please see our Linkedin post for more details and to sign up.
Image by midjourney: ”a photograph of a robot, sitting in a library, working on a jigsaw puzzle. The robot is spotlighted by light streaming in through a small window"