Threats: The Table of Contents
Like the Force, each threat has a light side, and a dark side.Let me share the table of contents for Threats. Each chapter is devoted to a threat. And like the Force, each threat has a light side and a dark side. For example, the book opens with Spoofing and Authenticity. But unlike the Force, we don't hope for balance. We hope to understand the threat, because that's the best way to anticipate and address the threat, and bring peace to the galaxy. (Or so we hope.)
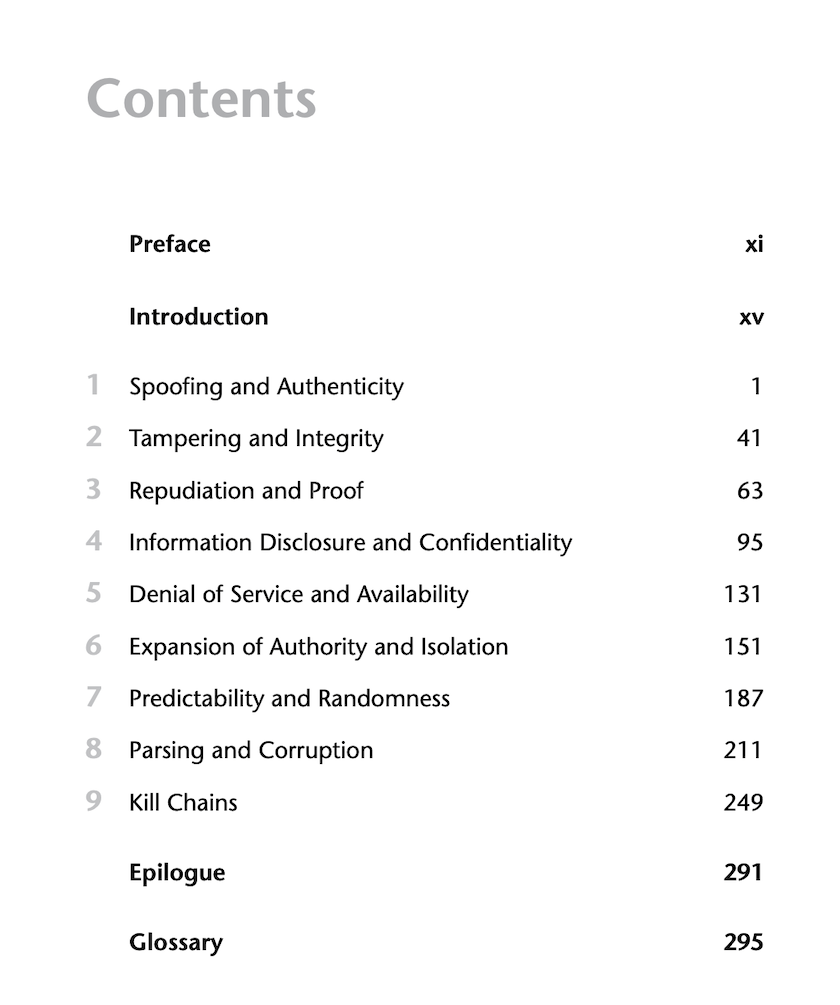
I'm excited that we have a simple table of contents that works as a quick guide to the book. It's common for technical books to have complex detailed tables of contents, but here, each chapter is structured the same:
- The threat
- Mechanisms
- Specific scearios or technologies
- Defenses
Many trees could have died to bring you that information. (There's also a bibliography and two indexes, because like the Force... no, that's not it. But there really is a second index, which I'll reveal soon.)
Threats: What Every Engineer Should Learn From Star Wars will be available January 25th wherever fine books are sold. You can pre-order on Amazon, Ada's Technical Books (my local technical bookstore), or bookshop.org.