Speculative Execution Threat Model
[no description provided]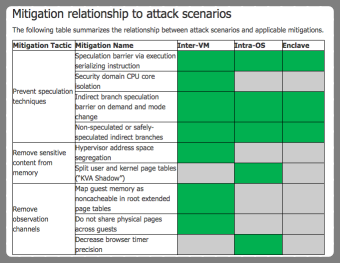
There's a long and important blog post from Matt Miller, "Mitigating speculative execution side channel hardware vulnerabilities."
What makes it important is that it's a model of these flaws, and helps us understand their context and how else they might appear. It's also nicely organized along threat modeling lines.
What can go wrong? There's a set of primitives (conditional branch misprediction, indirect branch misprediction, and exception delivery or deferral). These are built into gadgets for windowing and disclosure gadgets.
There's also models for mitigations including classes of ways to prevent speculative execution, removing sensitive content from memory and removing observation channels.