Threat Modeling Capabilities Released
A great new resource for threat modeling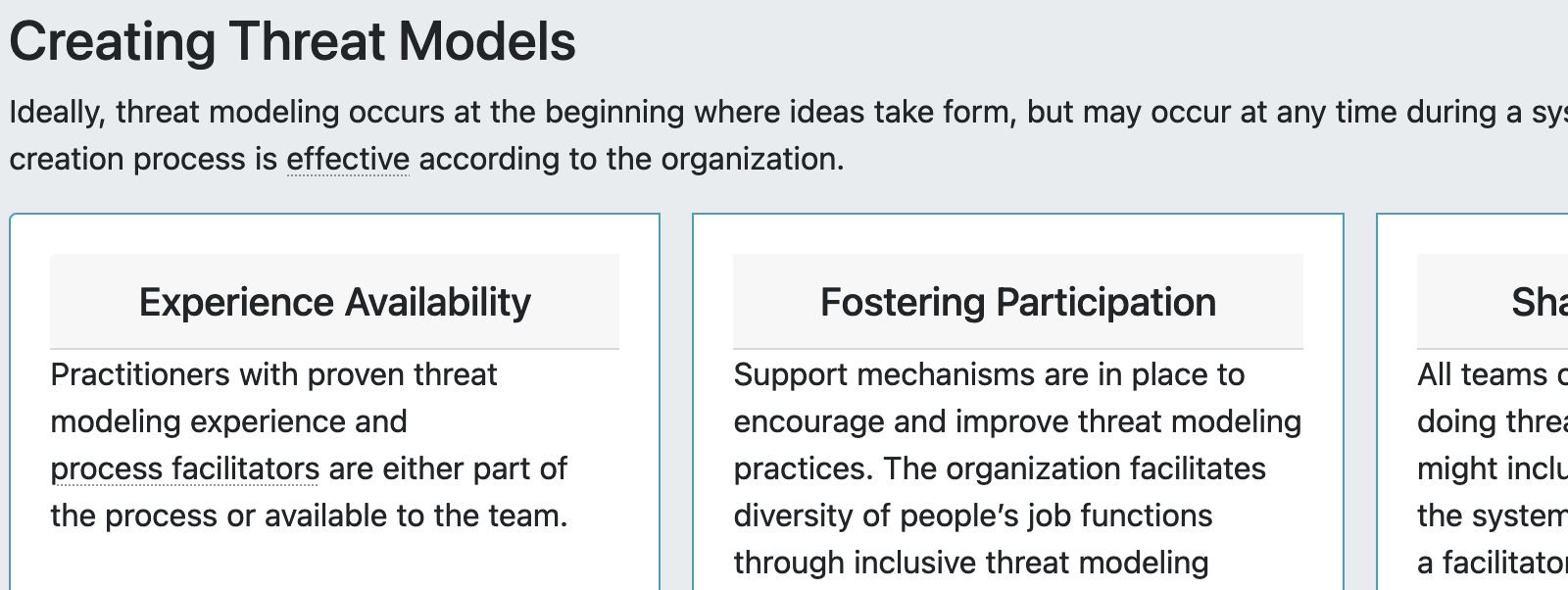
My collaborators on the Threat Modeling Manifesto have just released a set of Threat Modeling Capabilities. A capability delineates what an organization does. Others led this important work, and I don’t want to take much credit. I do think this fits into the “organizational” part of my Jenga Framework.
I’m really excited for this release because the document provides a way to think about a specific organization’s capabilities, and that means we can also talk about them and start to compare. It’s a very important step forward for effective threat modeling practice. If you threat model or run a threat modeling process, take a look. You can start to use this to answer the question “Are we doing a good enough job?” By design, we didn’t try to provide maturity scales.
Anytime there’s a document authored by 15 people, there are disagreements. I’m not a fan of the attackers bit for reasons I’ve written on extensively, most recently in Think Like Sieged-Sec. I’m also not a big fan of including risk: I think risk is informed by threat modeling and we should keep them conceptually separate, and that was hard in the context of a document like this.
My comments on attackers led to a lot of conversation, including:
- Think of actors in the “where does the attacker need to be” sense, not the threatintel sense.
- Similarly, think of both external and internal attackers. The latter might be unaware they’re breaking rules, especially in privacy.
- It’s important and tough to avoid getting fixated on what attackers are provably doing today. But if you’re fixated, you’re only locking barn doors after the horses have escaped.
But I appreciate that many of the folks involved did much more work than I did, and I share these not to cast shade, but to demonstrate that effective collaboration is a give and take process of rough consensus, which we achieved.