Artemis and Cybersecurity
Some thoughts on Artemis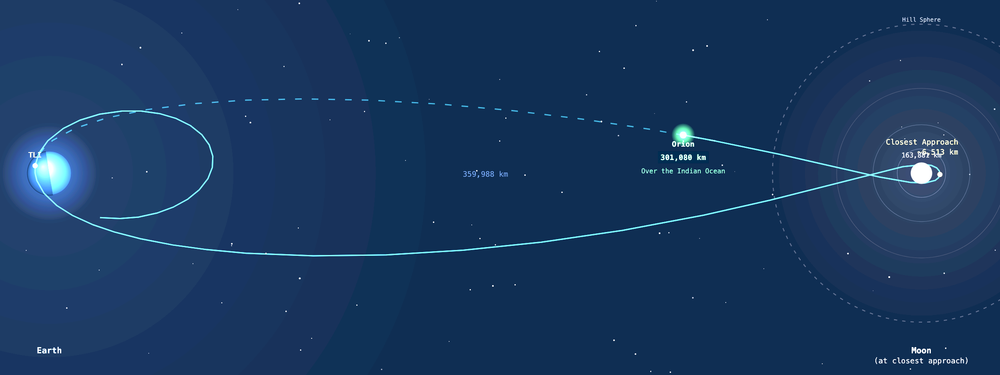
Like many people, I’ve spent the last days joyfully watching the Artemis mission, and wincing at some of the ways in which the computer technology is failing.
Before I get into that, I want to say that moon missions are one of the things that makes America great. There’s no other country that’s ever sent astronauts to the moon. And on this trip, we even made room for our Canadian neighbors. (Or is that Canadian neighbours?)
Engineering to go to the moon is incredibly hard. Every little bit is challenging, from temperature and pressure to lubrication. (One of the beautiful little Easter eggs in the lunar rover lego set is the stickers that say “wax.”) And the incredibly hard bits have to be integrated in with both physical and economic constraints.
Some of these, for example, the toilet, involve complicated dynamics of liquids at body temperature rapidly converting to ice, and clogging the lines.
But others seemed very much like the sorts of things that might have resulted from a failure to think about “what could go wrong?” I am hesitant to say that’s a contributing factor, because it’s easy to armchair quarterback and to misunderstand decisions that have been made. At the same time, there’s been a stream of failures of consumer-grade equipment (the Windows Surface computers, the GoPro cameras, and Outlook).
When I look at some of these, like the use of a PIN code, I wonder, is there an operational reason to have it? Outside of science fiction movies, there aren’t many places where you’re less likely to find an attacker than a space capsule. I bring this up because as we think about the security of space systems, we have to think about the security of the ground systems and IT support, where classical IT security is crucial, and the spacecraft, where there’s a different need to balance the security properties needed by the mission. In fact, as I type this, I’m watching a microphone problem seemingly delay a press conference. Availability is paramount, especially at crucial times like launch and re-acquisition of signal.

Security is a property of systems, and one that needs to be paid for. There are times when the requirements for that classic security and compliance with those rules can absorb energy that could otherwise be dedicated to mission-specific security.
Threat modeling is one of the analytic techniques we can bring to bear to understand those systems, and threat modeling has the advantage of being less heavyweight than some of the other techniques in use.
Finding the right combination of techniques to deliver appropriate security with appropriate assurance that the right work has been done well enough isn’t a matter of checklists or compliance and you’re done. It's a matter of bringing security into an engineering process in the right way for the organization, its existing processes and the mission on which they’re delivering.