Star Wars, Star Trek and Getting Root on a Star Ship
[no description provided]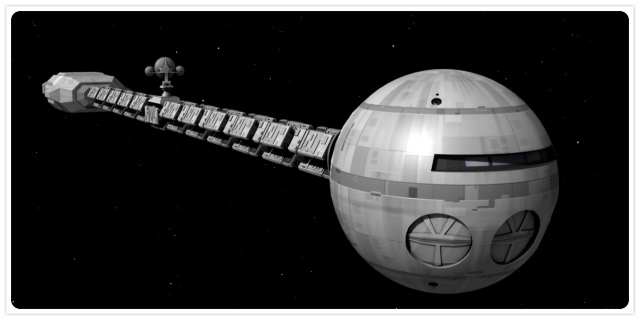
It's time for some Friday Star Wars blogging!
Reverend Robert Ballecer, SJ tweeted: "as a child I learned a few switches & 4 numbers gives you remote code ex on a 23rd century starship." I responded, asking "When attackers are on the bridge and can flip switches, how long a password do you think is appropriate?"
It went from there, but I'd like to take this opportunity to propose a partial threat model for 23rd century starships.
First, a few assumptions:
- Sometimes, officers and crewmembers of starships die, are taken prisoner, or are otherwise unable to complete their duties.
- It is important that the crew can control the spaceship, including software and computer hardware.
- Unrestricted physical access to the bridge means you control the ship (with possible special cases, and of course, the Holodeck because lord forgive me, they need to shoot a show every week. Scalzi managed to get a surprisingly large amount from this line of inquiry in Red Shirts. But I digress.)
I'll also go so far as to say that as a derivative of the assumptions, the crew may need a rapid way to assign "Captain" privileges to someone else, and starship designers should be careful to design for that use case.
So the competing threats here are denial of service (and possibly denial of future service) and elevation of privilege. There's a tension between designing for availability (anyone on the bridge can assume command relatively easily) and proper authorization. My take was that the attackers on the bridge are already close to winning, and so defenses which impede replacing command authority are a mistake.
Now, in responding, I thought that "flipping switches" meant physically being there, because I don't recall the episode that he's discussing. But further in further conversation, what became clear is that the switches can be flipped remotely, which dramatically alters the need for a defense.
It's not clear what non-dramatic requirement such remote switch flipping serves, and so on balance, it's easy to declare that the added risk is high and we should not have remote switch flipping. It is always easy to declare that the risk is high, but here I have the advantage that there's no real product designer in the room arguing for the feature. If there was, we would clarify the requirement, and then probably engineer some appropriate defenses, such as exponential backoff for remote connections. Of course, in the future with layers of virtualization, what a remote connection is may be tricky to determine in software.
Which brings me to another tweet, by Hongyi Hu, who said he was "disappointed that they still use passwords for authentication in the 23rd century. I hope the long tail isn't that long! 😛" What can I say but, "we'll always have passwords." We'll just use them for less.
As I've discussed, the reason I use Star Wars over Star Trek in my teaching and examples is that no one is confused about the story in the core movies. I made precisely this mistake.
Image: The Spaceship Discovery, rendered by Trekkie5000. Alert readers will recall issues that could have been discovered with better threat modeling.