Month of Owned Corporations
 Richard Bejtlich points to a very dangerous trend in his TaoSecurity blog, the “Month of Owned Corporations“:
Richard Bejtlich points to a very dangerous trend in his TaoSecurity blog, the “Month of Owned Corporations“:
Thanks to Gadi Evron for pointing me towards the 30 Days of Bots project happening at Support Intelligence. SI monitors various data sources to identify systems conducting attacks and other malicious activity. Last fall they introduced their Digest of Abuse (DOA) report which lists autonomous system numbers of networks hosting those systems.
SI published the latest DOA report Monday and they are now using that data to illustrate individual companies hosting compromised systems. They started with 3M, then moved to Thomson Financial, AIG, and now Aflac. For these examples SI cites corporate machines sending spam, among other activities. Brian Krebs reported on other companies exhibiting the same behavior based on his conversations with SI.
He irresponsibly spreads… Oh, heck. I can’t do it. This is great stuff. Let’s actually look at what networks are spreading junk. I like this as a start, and the weekly Digest of Abuse [link to http://blog.support-intelligence.com/2007/04/doa-week-14-2007.html no longer works] claims to look at:
We analized over 22,000 ASNs for every kind of eCrime including DDoS, Scanning, hosting Malware, sending Spam, hosting a phish, or transmitting virous.
Hmmm, so while I’m glad that they’re collecting and sharing data, what does it mean to be scanning? How do they define “hosting malware?” I really like the idea, and would suggest that Support Intelligence share more about what their data gathering methods look like, how they define each term, and how many of the incidents they see are of each type. (I’ve looked in their FAQ [http://www.support-intelligence.com/faq/], how it works [http://www.support-intelligence.com/technology/] page, and product tour [http://www.support-intelligence.com/services/].)
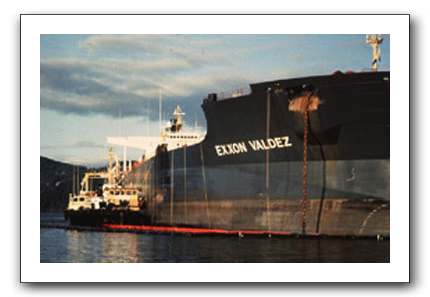
Photo: The Exxon Valdez, courtesy of the Alaska Fisheries Science Center. Why? Because talking about breaches helps get them noticed and cleaned up.
Thanks for the questions. I’ll take up the definitions you pointed out. As to hosts that host malware we have a number of sources for malware links including our own spam traps.
We take the binaries of these links and run them in a sandbox that we host on Amazon’s EC2. The sandbox provides us a report which we mine to see if the binary does anything evil. If it does something like contact a IRC c&c we list the source (or host) as a malware source.
there are many other items to define which I’ll work on putting something on our website so there is more transparency in our reporting.
-rick