Capture the Flag events and eSports
A breakdown of CTFs and eSports
Looking at what is popular with smaller niche crowds can give greater insight into the “next thing”. This natural selection of attention can inspire an evolution of methods and practices. Capture the Flag Events (CTFs) and electronic Sports (eSports) are good examples of a relatively new trend. I've had the chance to be front row with each in the past years and can say they both have vivid partisans. Spoiler alert! My conclusion is that CTFs are intrinsically an eSport with the attribute of having a strong educational value.
eSports, what is this millennial aberration?
Before jumping in to the “get off my lawn” reaction, I’d like you to picture an actual lawn within traditional sports. Usually it’s grass or some form of terrain where people are playing a game. It can have spectators either on-site or remote using a television. People are here to see action, to cheer for a team to achieve a goal or to win at the end. During a broadcast, commentators describe the game and do the animation of the overall spectacle.
Now take that, and imagine that for some people, the game is a video game and the lawn is a network.
Many eSports leagues exist around the world and important tournaments are broadcast online. The level of strategy, tactics and action can get heated and overwhelming. Commentators end up sounding like traditional sport announcers when shouting during intense moments. Spectators also fill arenas by the tens of thousands.
Winners return home with cash prizes that get pretty big, and with money coming from an industry that is bigger than the movie industry. This is where the level of competition broadens internationally. South Koreans are, more often than not, dominating in this respect.
Sponsors and gamers get paid to play, in what we call professional gaming. Those pro-gamers have this as their full-time job.
If your mind is not blown already, here’s a crowd of about six hundred people cheering for a video game to start. It was during a collective gathering of a StarCraft II tournament in 2011, called BarCraft Montreal.

Of course, not everyone is a pro. LAN parties and online competitions have also have places for amateurs. That phenomenon is even older than the broadcasting era. People playing video games in the 90s would sometime gather to compete for a cash prize. Back then, eSports was already a thing without having the name attached to it.
Fast forward to 2019, permanent venues and bars are now dedicated to the phenomena, with some great examples such as the eSports Arena in Las Vegas and Meltdown, an international franchise of eSports bars. Now stadiums fill with 20,000 spectators in North America during multi millions dollars gaming tournaments such as the Fortnite World Cup.
Capture the Flag events, a collective obsession
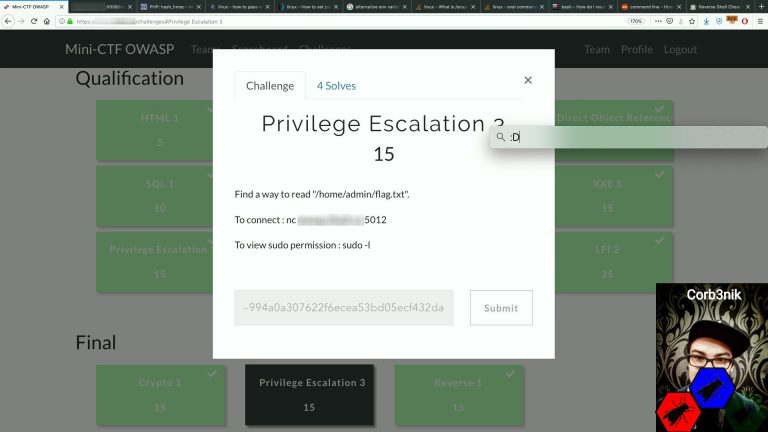
In the hacking communities, CTF events have always been the practitioner's favorite. It’s generally a tournament that spawns over hours if not a few days, where teams don’t fight each other, but rather solve problems with security related techniques. Challenges are usually presented within a defined category and their worth in awarded points is proportional to their difficulty. Sometimes, when the organizers want to put more effort in the presentation layer of the competition, a simulated scenario can be used. Common examples include hacking company X or being part of covert operations that goes against a dictatorial government. The kind of stuff hackers fantasize about. Regardless of the presentation, the goal is easy: to find flags. In other terms, you’re exploiting systems to gain information disclosure. The more you successfully hack, the more you get flags that gives points. The winning team is the one who gets the most points.
These kinds of events have existed for quite a very long time now, with my first personal participation being around 2002. CTFs have grown in popularity over time, with NorthSec being one of the biggest in North America at more than 700 people on-site.

Visually this looks similar to an eSports tournament, but the main difference is that most teams use Linux laptops instead of Windows gaming PCs.
The participants show equal amounts of passion for the subject matter, passing hours in front of their screen during the day to reach that good feeling of winning. In one case, it's finding a flag, and in another, it's to win a match against a competing team. When this happens, the sense of success doesn't only happen on the meta goal of winning the whole thing, but it also releases endorphins for every little gain that is made. Finding a flag is very rewarding!
Enough about games, here's something serious: Learning!
One of the undeniable effects of competing is that it makes people better at what they do. They push themselves further, they learn to improve. This is true in gaming, and especially true in CTF events.
In my opinion, a CTF event is one of the best ways to learn about offensive security and its impact. As the participants try to find ways of getting to the flag, they also teach themselves to work up to a successful kill chain. They have to construct the last step of exploitation that leads to the flag, thus gaining points from the impact of a successful attack. Instead of experiencing the stressful real-life scenario of a breach like a professional would, they have the dopamine release of winning. That's a pretty effective way to train a brain to reach a certain goal.
One important value of CTF challenges, versus real-life cases, is that the attacker understands there’s a final defined attack vector that is possible. The participant also might get a sense of the difficulty level by the amount of points associated with the flag. Additionally, flags can also have a category or name assigned, giving away the type of technique to use, such as "SQL Injection #2". This title is most certainly a good giveaway of the direction the attacker would need to take.
Competing by gathering more flags and points gives the contestant a motivation that is beyond the standard pentesting realm. More often than not, these end with running a Windows network exploitation tool and writing a report. This is somewhat less exciting than receiving a gold medal and applauds from a large crowd.
This type of motivation is palpable in the enthusiasm of participants. Go to any on-site event and see just how people are riveted to their screens and passionate about the results. There's a lot of team work involved and the social component of knowledge sharing is reinforced.
Professionals can use it to sharpen their skills, while more amateurish people can also gain satisfaction in hacking in a legalized and guided environment. This can be compared to the realm of online bug bounty, where the environment might have been legitimized for years, but has a natural lack of guidance for newcomers and some limitations on knowledge sharing.
In either artificial challenges or in real-case attacks, there's a common level of satisfaction to crack something open. The pleasure center of our brain are rewarded with accomplishment after working hard on a goal and reaching it. For the professional, the gains are also quicker and more frequent, as they can experience in hours what they would normally over weeks if not months.
CTFs effectively cover the full spectrum of skill levels. The top tier are looking to be challenged and win. Participants at the introductory level can use it to understand vulnerabilities and the impact of their exploitation. This is done on a first-hand basis, without getting into the overhead of a full-blown enterprise environment.
Aside from learning, the security industry can take advantage of the CTF event and use it as a recruiting mechanism. This especially benefits students as their cleverness and skills never cease to amaze in hacking. That might be not shown just by looking at their grades. Hacking and exploiting requires a certain amount of non-conformity and logical creativity which traditional schooling might never even test.
eSports + CTF = a new breed of edutainment
The art of hacking is difficult to grasp, as it requires a lot of learning and experimenting. One effective way people can improve is by observing others. If you are watching someone playing a game, and you analyze their strategy, you might improve your own just by observing. You will gain new tactics and strategies along the way. If you are lucky, you might even entertain yourself at the same time.
The whole concept of watching someone hacking is not fully exploited yet. Many step by step tutorial videos you can see online present ways of solving challenges, but leave out the exciting outcomes of a competition.
That is, until we did it back in 2015.

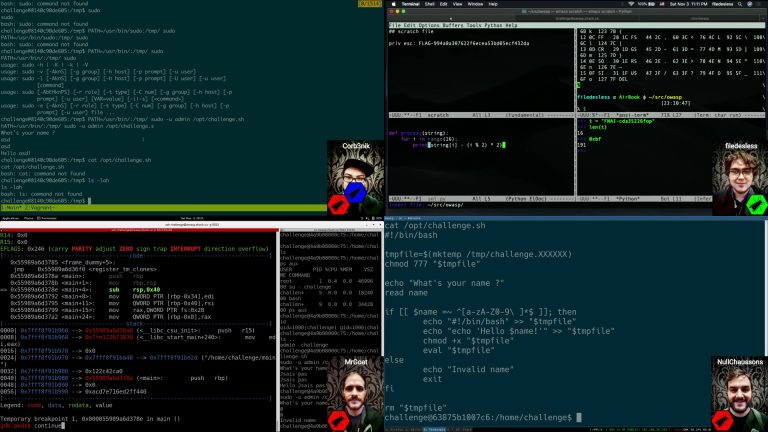
In order to be able to achieve it, we actually made a special CTF event with the main goal of broadcasting it. The initial part, which wasn't part of the main show, was a qualifying round where single contestants would participate in a classical CTF. This has assured us that the top ranked individuals brought to the finals would be the best. The final round was a few specially crafted CTF challenges designed to be presented in front of spectators. We asked those finalists, who were in another room, to share their screen so the on-stage presenters could comment on what is happening without spoiling the results. The challenges author came on stage to give the audience insights into solving some of them. We also even got some funny moments where the participants were talking to us through their console prompt. The whole session was very entertaining, as it gave the audience a true understanding of what a CTF is really about: a bunch of people searching on Google 😊.
Our last recorded efforts were in 2018, where we incorporated the flag scoring system into visuals and managed to have a full HD view of the participants.




This concept definitely captured the attention of CTF savvy people. A good part of the audience we had on-site were also competing in the qualifying round.
What we did is unparalleled as far as we know, but it needs to be refined, showcased and experimented more to reach a wider audience and gain its full potential. Publishing it online offers the chance of succeeding in popularity when taking into account the large number of views that a standard hacking tutorial normally gets.
Conclusion
Without an expansive introduction, the whole concept might look silly. But really, a CTF is a video game. Both share the same related components such as the competition aspect and the utilization of problem solving skills. They also share the fact that the action is done in front of a computer screen.
In a sense, CTF challenges are like a bunch of mini educational games. They give the participant a motivation to gain the computer security knowledge required to solve them and win.
One of the main barriers of acceptance on the edutainment concept is related to the fact that even the well established eSports phenomenons are still very much on the fringes for many people. Unfortunately, those same people could actually be more interested in computer security than in actual gaming.
Learning is all about expanding our mind. It can be done with self-service education to reach a goal or by being a spectator of other people technical skills. When people worrying about having perpetrators getting off their lawn (or network!) seek to expand their grasp on pieces of the hacking ecosystem, it can actually improve their overall understanding of computer security, and this could ultimately help them to threat model and defend their space better.